BluVector Proof of Concept: Advanced Threat Detection & Automated Threat Hunting
This PoC begins by detailing BluVector’s core product – Advanced Threat Detection (ATD) and how it expands visibility in your network traffic analysis by providing more quality analytics. This is done with multiple Machine-Learning Engines (MLEs) correlating all network events with Speculative Code Execution Engines (SCEs), probability & analytics engines, and other asset illuminators to prioritize threat notifications at line speed.
We then take the viewer on a journey into our newest product – Automated Threat Hunting (ATH) and how it can be used to correlate the threat landscape across your cloud and on-premise infrastructure. It produces and tracks the risk associated with all the entities that it identifies and enumerates in your network – and present and correlate adversarial campaigns across these entities. This specific portion of the PoC is from a real exercise that was conducted at the National Cyber Range and how ATH was able to put together a story around a Red Team attack, thus correlating the what, when, and how the system, entities, users, and other objects were attacked.
Related events
-

Cisco Proof of Concept: Network as Code! Automate VXLAN EVPN fabric with Ansible and DCNM
May 5, 2021, 3:00 pm ETSpring 2021 -

BlueCat Proof of Concept: One IPspace to Rule Them All Using the Power of Automation
May 6, 2021, 10:55 am ETSpring 2021 -

BluVector Proof of Concept: Advanced Threat Detection & Automated Threat Hunting
May 6, 2021, 7:45 am ETSpring 2021 -

Pensando Open Session – Connecting the Dots In The Modern Data Center
May 6, 2021, 12:30 pm ETSpring 2021 -

Cato Networks Proof of Concept: Cato Networks SASE Cloud In Action
May 5, 2021, 4:40 pm ETSpring 2021 -

Riverbed Open Session: The Future of Networking and Cybersecurity Across Complex Hybrid Environments
May 5, 2021, 4:45 pm ETSpring 2021 -

Pensando Academy: Establishing & Expanding Your Enterprise Source of Truth
May 5, 2021, 2:45 pm ETSpring 2021 -

Practical Considerations on the Road from Traditional to Cloud Native Enterprise Security: A Working Group Update
May 6, 2021, 5:15 pm ETSpring 2021 -

Orchestral.ai Proof of Concept: Autonomous Infrastructure: Connecting the Dots Between AIOps and Digital Transformation
May 6, 2021, 12:05 pm ETSpring 2021 -

Roundtable: Q&A featuring former AWS and Azure Global Black Belts in Networking
May 6, 2021, 11:50 am ETSpring 2021 -

Operations, Visibility, and Troubleshooting in the Public Cloud
May 6, 2021, 10:50 am ETSpring 2021 -

Roundtable: Lessons Learned Cloud Journey featuring former AWS and Azure Global Black Belts in Networking
May 5, 2021, 11:30 am ETSpring 2021 -

Cato Networks Academy: SASE and the Road to Network Transformation
May 6, 2021, 10:00 am ETSpring 2021 -

Cato Networks Open Session: SD-WAN for the Office vs. SASE for Everywhere
May 5, 2021, 12:00 pm ETSpring 2021 -

Pensando Proof of Concept: Accelerating MTTR in Any Environment
May 5, 2021, 12:35 pm ETSpring 2021 -

Pliant Proof of Concept: Driving Network Automation Using a Low Code Interface
May 5, 2021, 3:35 pm ETSpring 2021 -

Forward Networks Proof of Concept: Managing ACL Conflicts and Chaos
May 5, 2021, 12:20 pm ETSpring 2021 -

Cisco Academy: Engineering Kafka for Secure Autonomous Operation
May 6, 2021, 12:30 pm ETSpring 2021 -

Cisco Open Session: Extending the Cisco ACI Ansible Collection to Fit Your Need
May 5, 2021, 4:45 pm ETSpring 2021 -

VMware Proof of Concept: Implementing an AIOps Strategy with VMware Edge Network Intelligence
May 6, 2021, 11:15 am ETSpring 2021 -

PacketFabric Proof of Concept: Optimize Multi-Cloud Streaming Performance with PacketFabric Cloud Router
May 6, 2021, 11:55 am ETSpring 2021 -

Itential Proof of Concept: Delivering Rapid Time to Value Using Modular Automation Frameworks with the Itential Automation Platform
May 6, 2021, 10:20 am ETSpring 2021 -

VMware Open Session: Gaining visibility in your SASE rollout with AIops
May 5, 2021, 12:55 pm ETSpring 2021 -

Forward Networks Open Session: How a Digital Twin Will Make Your Network More Agile, Predictable, and Secure
May 5, 2021, 12:55 pm ETSpring 2021 -

Gluware Open Session: Gluware DevOps for NetOps: Automating and Integrating using APIs and Custom Data Models
May 5, 2021, 3:05 pm ETSpring 2021 -

Itential Open Session: Closing the Loop on Automation: Itential + Forward Networks
May 6, 2021, 2:20 pm ETSpring 2021 -

Itential Academy: Solving the Challenges of Automating Network Compliance Across Hybrid & Multi-Cloud Networks
May 6, 2021, 12:30 pm ETSpring 2021 -

Zscaler Proof of Concept: Enabling Enterprise Digital Transformation
May 5, 2021, 1:10 pm ETSpring 2021 -

NETSCOUT Proof of Concept: Using NETSCOUT Smart Data to Identify, Investigate, and Remediate Threats in Your Hybrid and Multi-cloud Deployments
May 5, 2021, 5:00 pm ETSpring 2021 -

Netone Systems Proof of Concept: Monitoring & Dynamic Policy Enforcement for Elastic Infrastructure
May 5, 2021, 1:25 pm ETSpring 2021 -

NetBrain Proof of Concept: Extending Automated Network Operations to Multi-Cloud Environments
May 5, 2021, 3:20 pm ETSpring 2021 -

Gluware Proof of Concept: Using Gluware to Automate Public Cloud IaaS
May 5, 2021, 2:45 pm ETSpring 2021 -

Alkira Proof of Concept: Build a Stress-free Network in the Cloud
May 5, 2021, 12:55 pm ETSpring 2021 -

Zscaler Open Session: Enabling Enterprise Digital Transformation – Illustrated
May 6, 2021, 2:20 pm ETSpring 2021 -

Alkira Open Session: Building Your Next-Gen Network for the Cloud Era
May 6, 2021, 12:30 pm ETSpring 2021 -

NETSCOUT Open Session: Network Visibility for Unified Security and Assurance in the Multi-Cloud
May 5, 2021, 12:55 pm ETSpring 2021 -

Cloud Native DevOps and Digital Transformation: Today and Tomorrow
May 6, 2021, 3:25 pm ETSpring 2021 -
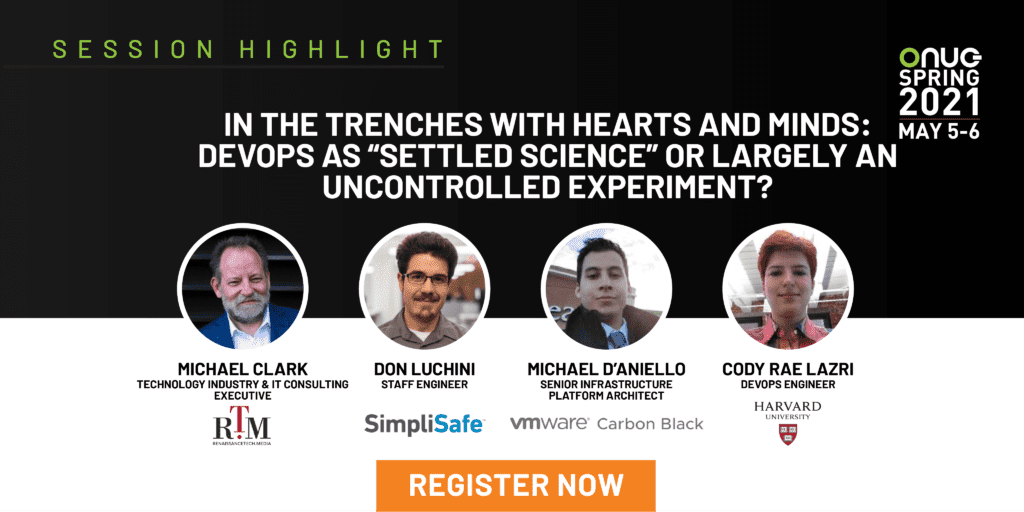
In the Trenches with Hearts and Minds: DevOps as “Settled Science” or Largely an Uncontrolled Experiment?
May 6, 2021, 5:15 pm ETSpring 2021 -

Creating a Standardized Security Information Model To Streamline Security Infrastructure
May 5, 2021, 9:35 am ETSpring 2021 -

Public Cloud: Just More Hype Or A Permanent Change In Computing?
May 6, 2021, 9:30 am ETSpring 2021 -

Integrating Enterprise Telemetry and AI/ML to Deliver Real-World Data Center Automation – Pensando Keynote Presentation
May 6, 2021, 3:05 pm ETSpring 2021 -

Accelerate Your Digital Transformation with Zero Trust – Zscaler Keynote Presentation
May 6, 2021, 2:45 pm ETSpring 2021 -

Building an Elastic Network Infrastructure with Global SASE – Vitesco Technologies with Cato Networks Keynote Presentation
May 6, 2021, 9:10 am ETSpring 2021 -
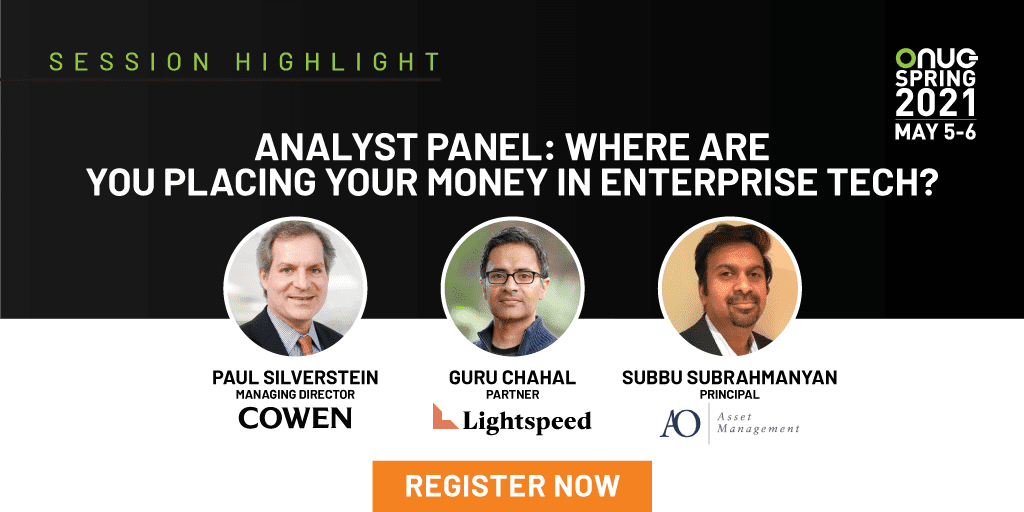
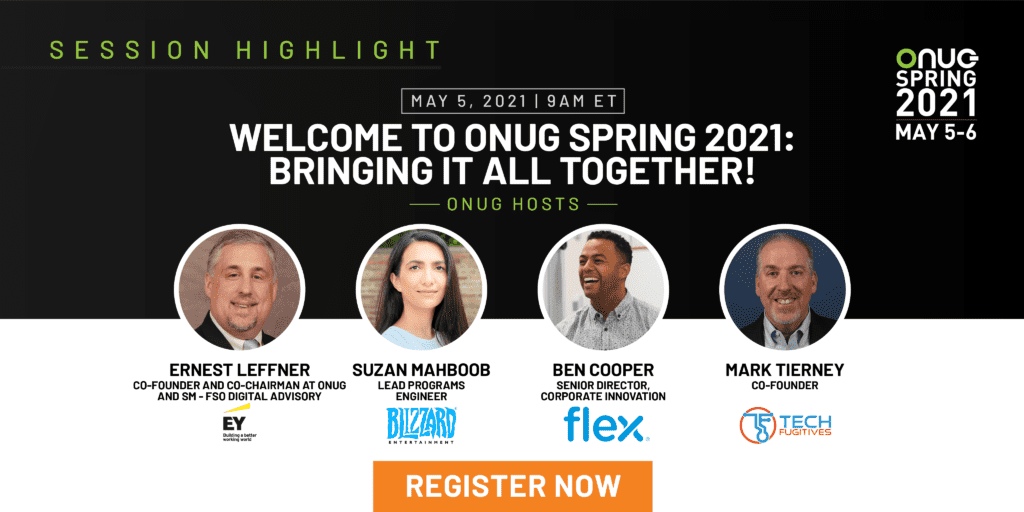
Analyst Panel: Where Are You Placing Your Money in Enterprise Tech?
May 5, 2021, 3:35 pm ETSpring 2021 -

Achieving “Same Day” Delivery of Network Services Through Automation – S&P Global with Itential Keynote Presentation
May 5, 2021, 2:20 pm ETSpring 2021 -

Born-in-the-Cloud Tekion Accelerates Business with Alkira Network Cloud – Tekion with Alkira Keynote Presentation
May 5, 2021, 2:00 pm ETSpring 2021 -

You Asked For It, and You Got It, Now What Do You Do With It? Telemetry in the Cloud Era
May 5, 2021, 12:20 pm ETSpring 2021 -

Elastic Infrastructure: Re-defining the Process for Enabling People and Applications for the Future
May 6, 2021, 12:55 pm ETSpring 2021 -

Transforming a Global Enterprise to a Fully Automated State – EY with Gluware Keynote Presentation
May 5, 2021, 1:40 pm ETSpring 2021 -

Orchestration and Automation Is Now Driving Underlay Infrastructure Purchasing Decisions
May 6, 2021, 1:45 pm ETSpring 2021